We already talked about AD infrastructure and common AD objects. Now let’s see how to install a domain controller using Windows Server 2012.
In the older versions of Windows Server we would go to command prompt and type dcpromo. That doesn’t work anymore and we will get this warning if we try to do that.
We see that the domain services installation wizard is now relocated to Server Manager. So, we don’t do the command line version of that anymore. Now we go to Add Roles and Features option in Server Manager.

Everything that we need to install the domain controller is included in this. If we already have an existing domain, for example, Windows Server 2008 domain controller and now we want to add a Windows Server 2012 domain controller to that existing domain. When we join this Windows Server 2012 domain controller to the existing domain it will now automate a lot of things that we had to do manually. For example, when we upgrade from Windows Server 2003 to 2008, you have to run a adprep /forestprep and adprep /domainprep. That would actually modify the active directory schema of the old 2003 active directory to the 2008 active directory. We had to do that because the schema is the structure of active directory that defines how objects are created and managed.
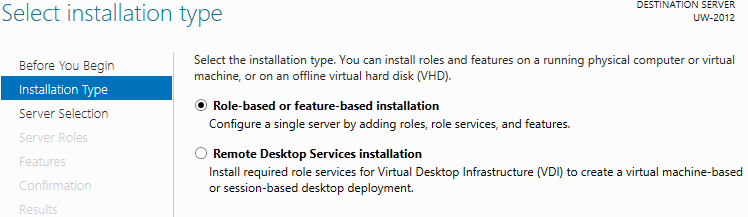
Now that’s all included in Add Roles and Features option. Let’s do that now. We’ll click Next on the Before You Begin page. On the next screen we’ll choose the Role-based or feature-based installation for our local computer.

On the next screen we choose the server. We only have one server here but later when we have a domain involved we can add a bunch of different servers here, and we can actually do the same function on multiple servers at once.

On the next screen we will check the box for Active Directory Domain Services. When we do that, the following windows will appear.

We see that this tool will automatically add other tools that we will need. We can click OK and Next until we get to the Install button.

Once the wizard has completed notice we can select to promote this server to a domain controller

But if we forget to click it here, we can go to AD DS where we’ll see a warning that configuration is required for active directory domain services. We can click on ‘more’ and choose to promote this server to a domain controller.


Now we have several option. We can add a domain controller to an existing domain, for example if we already had a Windows Server 2008 domain in place. We can also add a new domain to an existing forest. We would do that if we wanted to create a child domain. We are not at that stage yet because we don’t even have a root domain yet. So, we are going to select the “Add a new forest” option and enter our root domain name.

On the next screen we choose a forest and a domain functional level. Think of functional levels as how many features we get in that in our active directory infrastructure. If we were adding additional domain to an to an existing forest or adding additional domain controller for example, we could could choose a down level forest or domain functional level.

When we go down on a functional level, we loose some of the new features that comes with new server versions, but we get compatibility with existing environment.
Also, we need to have a DNS server (Domain Name System server) because active directory is fully integrated with DNS. We will also make our server a global catalog. This means that it will contain objects from every domain in our forest. We also see a read-only domain controller option. In short, that allows us to install a domain controller that would be a read-only, meaning that we could not create or modify accounts on that domain controller.
We also need to provide a Directory Services Restore Mode password. This is a password that will be used in case of troubleshooting active directory. When something is not working properly we can boot into a directory services restore mode using the administrators directory services restore mode password.
Once we click Next, we see a warning telling us that a parent zone can’t be found. That’s OK because we’re creating a parent zone right now, so we can click next.

Next, server will check our network to see if it can find a NetBIOS name called UTILIZEWINDOWS, and if it can’t, it will allow us to click on next.

On the next screen we will see where we store various components of active directory. We will stick with the defaults here, but if we want to store them elsewhere. we can.

The next screen is a summary of our selections. Here we can click on the View Script option, which will show us Power Shell commands used to do all our selections. We can save it and use it in future if we want, for example, to create multiple domains of child domains, etc., simply by changing particular options. Note that the script uses back tick (`) which allows us to enter different instruction on separate lines, but will provide the same execution as if all of them are written on the same line.

OK, let’s click next where prerequisites will be checked.

We see several messages. The first is related to an old NT 4.0 compatibility issue, where if we had to make it compatible with NT 4.0, we had to weaken security. We don’t do that any more. The second is the DNS issue we already mentioned. So, if we see a red symbol here, we can’t proceed at that point. We can try to go back and fix it and then rerun the prerequisites check.
In our case we can continue with the installation of active directory domain services. After the installation, in our Server Manger we will now see AD DS and DNS items.
Let’s check the DNS briefly. We will select the DNS option from the Server Manger, select our server, right-click it and select DNS Manger option.

We could also go to Tools and choose DNS there. Anyway, when we open this up, we’ll see our new forward lookup zone. The only object created so far is our server itself (uw-2012), which has a host record.

This means that we can now locate it by using the Fully Qualified Name of uw-2012.saadz26.sg-host.com. This will take us to the IP address of 192.168.62.10.
OK, let’s check now the AD DS in our Server Manger. Here, again we can right-click our server and choose the tool we want to manage.

One common tool is Active Directory Users and Computers. The first things that we will want to do in a new domain is to create an organizational unit (OU) to put our user accounts in and our computer accounts. To create OU, we can right-click on our saadz26.sg-host.com server, select New, and choose to add a new organizational unit.

We will name it UW Users.

When that is created, we can add a user to it. To do that, right-click it and select New -> User. We will enter name and log on name for our user.


On the next screen we have to define some password for our user.

Note that the default option is to make user change his password on the next log on, which is great so we no longer know the password for the user. We can also choose choose that user cannot change password, which is what we can do for service accounts. If the service account ever gets compromised we don’t want it to be able to change the password and prevent the service from running anymore. Most services require some kind of an account to be associated with in order to have the authority to be to run. “Password never expires” option can also be used with a service account, since we don’t usually want the password to expire after some time because then all the services would stop running. We also have a “Account is disabled” option, which can be used if the account won’t be used immediately, for example.
Now that the user is created, we can double-click it, and we will see all kinds of additional things we can enter for it.

We can only have those fields available once the account is created.
Ok, we now have our Directory Services enabled. The next thing is to add our workstations to our new domain.