This article is about a series of network troubleshooting tools that you can use in command prompt to troubleshoot and gather information about your network. We’re going to go over four commands: “ipconfig”, “nslookup”, “ping”, and “tracert”.
ipconfig
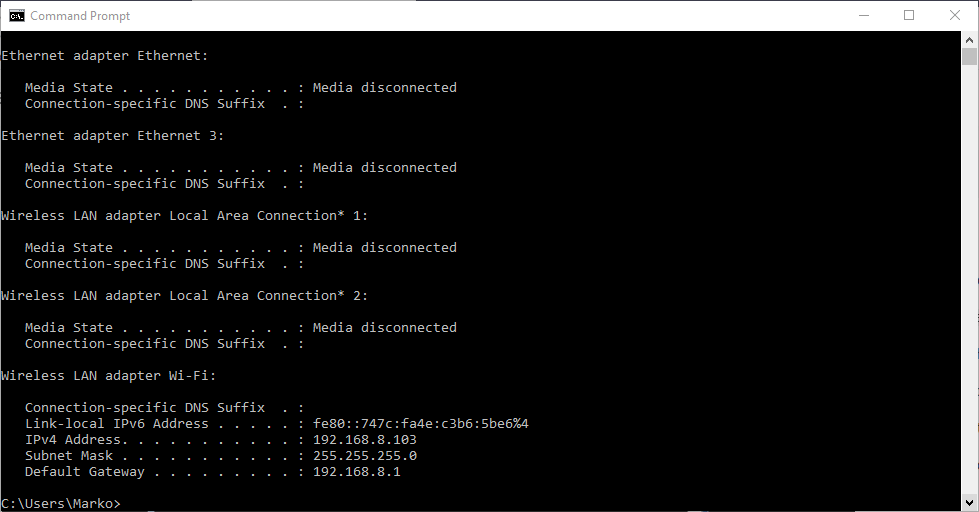
The “ipconfig” displays the current information about your network such as your your IP and MAC address, and the IP address of your router. It can also display information about your DHCP and DNS servers. Let’s see the basic output of “ipconfig”:
Depending on your network connection type, you may see different output for different connection. For example, if you are connected to the network using Ethernet (you plug in your network cable to the RJ45 jack), you’ll see IP information in the “Ethernet adapter” section. In our case we are connected to the WIFI (wireless) connection so we our information there. In our case, the local IP (IPv4) of our computer is 192.168.8.103. We also see the Subnet Mask (255.255.255.0) which we can use to find the network address. We also see the Default Gateway IP (192.168.8.1), which is our router
However, we don’t see DHCP and DNS information. To see detailed IP information we can use the “/all” switch together with “ipconfig” command (ipconfig /all).
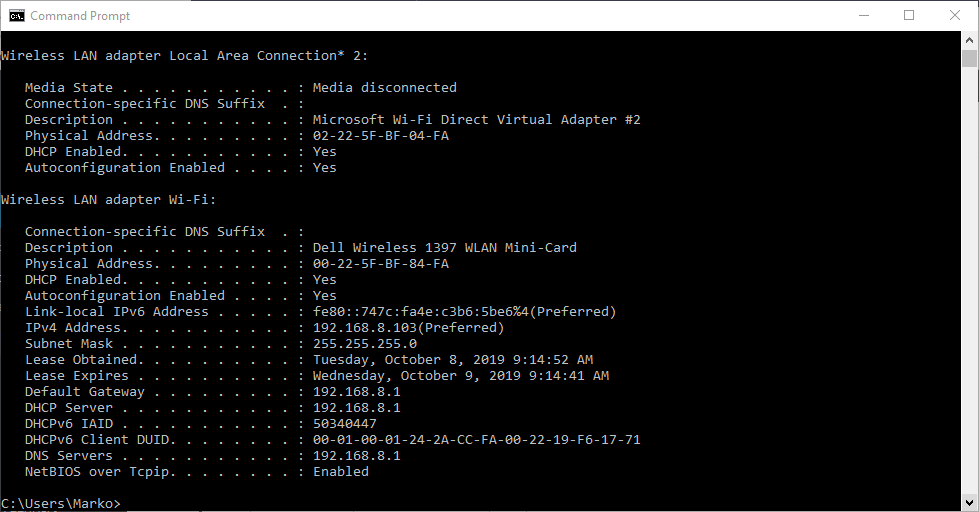
This time there’s much more information present. The IP address, the Subnet Mask and and the Default Gateway address is still here, but this time you can also see your DHCP server and DNS server. In our case the DHCP IP address is the same as the router address, which means that DHCP server is currently residing on the router. DNS server is also the same as router address which means it is also DNS server.
Information gathering is a part of troubleshooting. For example, if you’re trying to troubleshoot the DNS server, you can beforehand type in the “ipconfig” command and find where the DNS server is.
Network troubleshooting with ping
The “ping” command ping command allows you to send a signal to another device, and if that device is active, it will send a response back to the sender. The “ping” command is a subset of the ICMP (Internet Control Message Protocol), and it uses what is called an “echo request”. So, when you ping a device you send out an echo request, and if the device you pinged is active or online, you get an echo response.
For example, if your local computer has Internet connectivity issues, you can try to ping your router. If you get no response then you know that the router is what is giving you problems. Let’s ping our router IP, which is 192.168.8.1 in our example, and let’s analyze the the printout.

What happens is we send out four packets to the destination and the destination responds back with the same four packets. We sent out 32 bytes of data and we got back 32 bytes of data, and we got it back in 9 milliseconds average. From this we see that the device is alive and see the connection stability (4 of 4 packets received). Let us ping www.google.com and see what happens.

We got a similar printout, however, since we used domain name, we now see the resolved IP address of www.google.com. We sent out 32 bytes of data but, because Google server is far away it took 82 milliseconds to send and receive 4 packets from Google. We sent and received 4 packets so the connection was stable. Finally let’s ping a device that doesn’t exist.

We get a “Request timed out” response. This is going to yield the same kind of results if a device wasn’t actually working. As you can see at the summary, wee sent four and received zero, so it was a hundred percent lost. That means the system you’re trying to reach is not connected to the network.
tracert
This command lets you see all steps a packet takes to the destination. For example, if we send a packet to www.google.com, it actually goes through a couple of routers to reach the destination. The packet will first go to your router, and then it will go to all kinds of different routers before it reaches Google servers. We can also use the term “hops” instead of routers. Let’s run the command and see what kind of results we get.
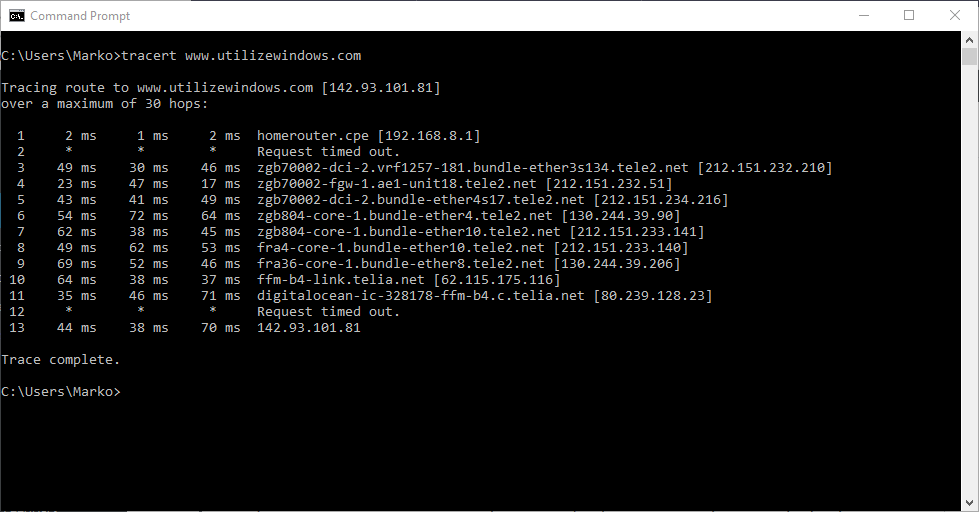
We have traced the route to www.saadz26.sg-host.com, and we’re getting a list of each of the routers that we’re hitting. At the end we see the IP address for saadz26.sg-host.com server so the trace is complete. In our case we have 13 hops before we actually reached the intended server. The first router that we hit was our own router (we can tell by the IP address 192.168.8.1).
So what is the significance of this? Let’s say your home network was perfectly fine but there was a problem with some router in the between, for example with your ISP router. If there’s any problems it will try to indicate what the problem is. It could say things like “request timed out”, “destination unreachable” or similar. However, different messages don’t necessarily mean that there is a real problem with the device. There are several reasons why a “Request timed out” message may appear at the end of a trace route. This is typically because a device doesn’t respond to ICMP or traceroute requests. Also, the device firewall or other security device could be blocking the request. Here is article with more details about tracert command.
nslookup
The nslookup command will fetch the DNS records for a given domain name or an IP address. Remember the IP addresses and domain names are stored in DNS servers, so the nslookup command lets you query the DNS records to gather information.
Let’s say you wanted to know the IP address of www.saadz26.sg-host.com. You could simply type in nslookup and type in www.saadz26.sg-host.com. Let’s analyze this printout.

The first two lines show you which DNS server was used to get these results. Our DNS server happens to reside on our router, so our router is also our DNS server. The answer that we got was the IP address of the www.saadz26.sg-host.com server.